Cyber Weekly Flash Briefing 09 October 2020: Jersey based insurance firm Ardonagh hit with ransomware; Boards increase cyber investment; spike in romance scams; Amazon Prime Day phishing spike
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
Jersey based insurance firm Ardonagh Group disabled 200 admin accounts as ransomware infection took hold
Jersey-headquartered insurance company Ardonagh Group has suffered a potential ransomware infection.
Reports indicated that the insurance firm had been forced to suspend 200 internal accounts with admin privileges as the "cyber incident" progressed through its IT estate.
The UK's second largest privately owned insurance broker, according to the Financial Times, Ardonagh Group has spent the year to date acquiring other companies.
The timing of the most recent attack is unfortunate: Ardonagh recently published its financials, showing a loss of £94.m, according to reports.
Why this matters:
Whilst there is nothing to suggest these attacks are linked this attack comes a week after US insurance giant Gallagher was also hit with ransomware.
No firm is immune to being hit with ransomware, no matter how good they think their defences are, and then it comes down to how well you had planned for ransomware happening and how capable you are to recover and get the business back on its feet.
Read more: https://www.theregister.com/2020/10/06/ardonagh_group_ransomware/ and https://www.insurancetimes.co.uk/news/ardonagh-data-breach-reported-to-information-commissioner/1434888.article
Boards Increase Investment in Cyber security in Face of Threats and Regulatory Fines
Board decisions on cyber security spending are slowly improving following the impact of regulatory fines and COVID-19.
According to research surveying 908 senior IT security decision makers working within organisations with more than 500 employees, 58% plan to add more security budget in the next 12 months.
Amid growing cyber threats and rising risks through the COVID crisis, CISOs report that boards are listening and stepping up with increased budget for cyber security, with 91% agreeing that their board adequately supports them with investment.
Retro-fixing of security to remote working tools was “a path and direction most organisations have been going down, however it was always a lower priority.”
COVID-19 has accelerated the investment into both cloud and remote working budgets, and this includes the need for secure remote access and the ability to access from any location. Having a CISO on the board is helping ensure technology that supports remote working environments are also secure by design.
Why this matters:
Boards are definitely listening and stepping up with increased budget for cyber security, however many firms still tend to view any investment as a cost rather than adding business value. There is still some way to go, boards mainly approve investments after a security incident or through fear of regulatory penalties for non-compliance which shows that cyber security investment decisions are more about insurance than about any desire to lead the field which, in the long run, limits the industry’s ability to keep pace with the cyber-criminals.
Read more: https://www.infosecurity-magazine.com/news/boards-increase-investment-fines/
Online Romance Scams Spike Under Lockdown
Police and banks are celebrating after revealing that £19 million in fraud was stopped in the first half of the year, although romance scams are reportedly on the rise.
Over 600 reports of romance scams were made each month in June, July and August, contributing to a 26% year-on-year increase in cases recorded by Action Fraud, according to Sky News.
These are typically confidence tricks where a vulnerable individual is contacted via a dating site and financially exploited or unwittingly used as a money mule.
Why this matters:
Over 19,400 such crimes were logged with the FBI last year, making it the second highest earner for cyber-criminals after business email compromise (BEC). Over $475 million was lost to romance scammers in 2019, the law enforcement agency said.
In the UK, losses are said to have exceeded £66 million between August 2019 and August 2020. As a result, various dating sites, banking groups and police are running a “Take Five” awareness campaign designed to warn users of the dangers posed by internet scammers.
The spike in romance scams coincided with COVID-19 lockdowns in the UK and much of the rest of the world, and a subsequent shift in crime and fraud online.
Action Fraud claimed it saw an increase in reported attacks in the first month of lockdown, to nearly 4000. UK Finance last month claimed that fraudsters are increasingly shifting their operations online.
However, Action Fraud also revealed this week that millions of pounds worth of fraud has been prevented so far this year thanks to a Banking Protocol first introduced three years ago.
The initiative enables banking staff in branches to alert their local police force when they suspect a customer is being scammed, for example if they are transferring or withdrawing large sums of money. It has been used to good effect to stop romance fraud, and impersonation scams, Action Fraud claimed.
In addition to the £19.3 million in fraud allegedly prevented, 100 arrests were made in the first half of the year.
Read more: https://www.infosecurity-magazine.com/news/online-romance-scams-spike-under/
WEF: Cyber-Attacks Remain Top Business Risk in the West
Cyber-attacks have dropped down the pecking order in terms of top global business risks but remain high on the priority list in North America and Europe, according to the latest World Economic Forum (WEF) data.
The annual Regional Risks for Doing Business report is compiled from over 12,000 responses from business leaders in 127 countries. They are presented with a pre-selected list of 30 global risks and asked to choose the five that they believe to be of most concern for doing business in their country over the next decade.
Why this matters:
Unsurprisingly given the current financial and healthcare crisis, the top two global risks were unemployment and spread of infectious disease, followed by fiscal crisis. Spread of infectious disease also topped the priority list for business leaders regionally in Europe, Eurasia and East Asia and the Pacific.
However, although cyber-attacks fell from second place globally last year to fourth, they are still top-of-mind in the West.
They were named the number one risk of the next decade by North American business leaders, garnering a share of 55% versus infectious diseases in second with 30%. Cyber-risk was placed second in Europe but first in the UK, with 56% versus fiscal crises in second with 45%.
Read more: https://www.infosecurity-magazine.com/news/wef-cyberattacks-top-business-risk/
Ransomware: Surge in attacks as hackers take advantage of organisations under pressure
The number of ransomware attacks has significantly grown over the past few months as cyber criminals look to cash in on security vulnerabilities opened up by the rise in remote working.
Researchers at cyber security company Check Point said the number of daily ransomware attacks across the globe has increased by half over the past three months – and that they've almost doubled in the US.
Why this matters:
One of the reasons ransomware attacks are on the rise is because of the swift switch to remote working that has forced many people to work from home for the first time, something that could leave them vulnerable to phishing emails and malware attacks, especially on a home network that likely won't be as secure as an enterprise environment.
Working from home also makes monitoring devices for malicious activity harder for information security teams than it would be if every user was under one roof, providing hackers with a better chance of going about their business unnoticed.
Amazon Prime Day Spurs Spike in Phishing, Fraud Attacks
Cyber criminals are tapping into Amazon’s annual discount shopping campaign for subscribers, Prime Day, with researchers warning of a recent spike in phishing and malicious websites that are fraudulently using the Amazon brand.
There has been a spike in the number of new monthly phishing and fraudulent sites created using the Amazon brand since August, the most significant since the COVID-19 pandemic forced people indoors in March, according to a new report published this week.
Why this matters:
As shoppers gear up for two days of great deals, cyber criminals are preparing to prey on the unwary, taking advantage of those who let their guard down to snap up bargains.
Prime Day actually happens over two days—this year the event falls on Oct. 13 to 14. Amazon Prime customers enjoy special sales and discounts on top brands to mark the biggest shopping event of the year on the online retail giant’s site.
Amazon last year yielded over $7 billion in sales during the 36-hour event, which could go even bigger this year due to “the decline of brick and mortar retail and the close proximity to the holidays,” researchers noted. Indeed, mandatory stay-at-home orders globally that began with the COVID-19 pandemic in March have significantly boosted Amazon’s business, a trend that shows no signs of abating.
Read more: https://threatpost.com/amazon-prime-day-spurs-spike-in-phishing-fraud-attacks/159960/
Microsoft warns of Android ransomware that activates when you press the Home button
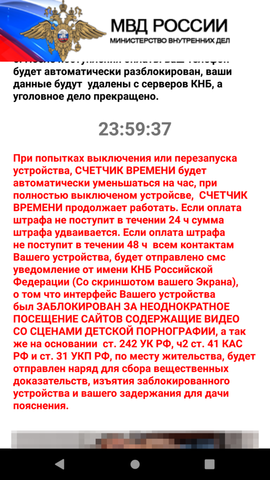
A new strain of mobile ransomware abuses the mechanisms behind the "incoming call" notification and the "Home" button to lock screens on users' devices.
Named AndroidOS/MalLocker.B, the ransomware is hidden inside Android apps offered for download on online forums and third-party websites.
Just like most Android ransomware strains, MalLocker.B doesn't actually encrypt the victim's files but merely prevents access to the rest of the phone.
Once installed, the ransomware takes over the phone's screen and prevents the user from dismissing the ransom note — which is designed to look like a message from local law enforcement telling users they committed a crime and need to pay a fine.
Why this matters:
Ransomware posing as fake police fines has been the most popular form of Android ransomware for more than half a decade now.
Across time, these malware strains have abused various functions of the Android operating systems in order to keep users locked on their home screen.
Past techniques included abusing the System Alert window or disabling the functions that interface with the phone's physical buttons.
MalLocker.B comes with a new variation of these techniques.
The ransomware uses a two-part mechanism to show its ransom note.
The first part abuses the "call" notification. This is the function that activates for incoming calls to show details about the caller, and MalLocker.B uses it to show a window that covers the entire area of the screen with details about the incoming call.
The second part abuses the "onUserLeaveHint()" function. This function is called when users want to push an app into the background and switch to a new app, and it triggers when pressing buttons like Home or Recents. MalLocker.B abuses this function to bring its ransom note back into the foreground and prevent the user from leaving the ransom note for the home screen or another app.
The abuse of these two functions is a new and never-before-seen trick, but ransomware that hijacks the Home button has been seen before.
Suspected Chinese Hackers Unleash Malware That Can Survive OS Reinstalls
Chinese hackers may be using malware that can survive Windows OS reinstalls to spy on computers.
Security firm Kaspersky Lab uncovered the malware, which exploits a computer’s UEFI (Unified Extensible Firmware Interface) to continually persist on a Windows machine.
Why this matters:
Attacking the UEFI is pretty alarming because the software is used to boot up your computer and load the operating system. It also operates separately from your computer’s main hard drive, and usually resides in the motherboard’s SPI flash memory as firmware. As a result, any malicious process embedded in the UEFI can survive an operating system reinstall while evading traditional antivirus solutions. This attack shows that in exceptional cases actors are willing to go to great lengths in order to gain the highest level of persistence on a victim’s machine.
New HEH botnet can wipe routers and IoT devices
A newly discovered botnet contains code that can wipe all data from infected systems, such as routers, servers, and Internet of Things (IoT) devices.
Named HEH, the botnet spreads by launching brute-force attacks against any internet-connected system that has its Telnet ports (23 and 2323) exposed online.
If the device uses default or easy-to-guess Telnet credentials, the botnet gains access to the system, where it immediately downloads one of seven binaries that install the HEH malware.
Why this matters:
This HEH malware doesn't contain any offensive features, such as the ability to launch DDoS attacks, the ability to install crypto-miners, or code to run proxies and relay traffic for bad actors.
The only features present are a function that ensnares infected devices and coerces them to perform Telnet brute-force attacks across the internet to help amplify the botnet; a feature that lets attackers run Shell commands on the infected device; and a variation of this second feature that executes a list of predefined Shell operations that wipe all the device's partitions.
US Department of Homeland Security (DHS) warns that Emotet malware is one of the most prevalent threats today
The malware known as Emotet has emerged as “one of the most prevalent ongoing threats” as it increasingly targets state and local governments and infects them with other malware, the cybersecurity arm of the Department of Homeland Security said on Tuesday.
Why this matters:
Emotet was first identified in 2014 as a relatively simple trojan for stealing banking account credentials. Within a year or two, it had reinvented itself as a formidable downloader or dropper that, after infecting a PC, installed other malware. The Trickbot banking trojan and the Ryuk ransomware are two of the more common follow-ons. Over the past month, Emotet has successfully burrowed into Quebec’s Department of Justice and increased its onslaught on governments in France, Japan, and New Zealand. It has also targeted the Democratic National Committee and numerous other US state and local government agencies.
Hackers exploit Windows Error Reporting service in new fileless attack
A new fileless attack technique that abuses the Microsoft Windows Error Reporting (WER) service is the work of a hacking group that is yet to be identified.
According to researchers the attack vector relies on malware burying itself in WER-based executables to avoid arousing suspicion.
In a blog post on Tuesday the researchers said the new "Kraken" attack -- albeit not a completely novel technique in itself -- was detected on September 17.
A lure phishing document found by the research team was packaged up in a .ZIP file. Titled, "Compensation manual.doc," the file claims to contain information relating to worker compensation rights, but when opened, is able to trigger a malicious macro.
Why this matters:
The macro leads to a payload injected a process connected to the WER service and used by Microsoft to track and address operating system errors.
That reporting service, WerFault.exe, is usually invoked when an error related to the operating system, Windows features, or applications happens," Malwarebytes says. "When victims see WerFault.exe running on their machine, they probably assume that some error happened, while in this case they have actually been targeted in an attack.