Threat Intelligence Blog

Contact us to discuss any insights from our Blog, and how we can support you in a tailored threat intelligence report.
Black Arrow Cyber Threat Briefing 23 April 2021
Black Arrow Cyber Threat Briefing 23 April 2021: Cyber Attacks Rise For Businesses, Pushing Many To The Brink; MI5 Warns Of Spies Using LinkedIn To Trick Staff; Sonicwall Warns Customers To Patch 3 Zero-Days Exploited In The Wild; FBI Removed Backdoors From Vulnerable Exchange Servers, Not Everyone Likes The Idea; Pulse Secure VPN Zero-Day Used To Hack Defense Firms & Govt Orgs; Solarwinds Hack Could Cost Insurance Firms $90M; Mount Locker Ransomware Aggressively Changes Up Tactics; QR Codes Offer Easy Cyber Attack Avenues as Usage Spikes
Welcome to this week’s Black Arrow Cyber Threat Briefing – a weekly digest, collated and curated by our cyber experts to provide senior and middle management with an easy to digest round up of the most notable threats, vulnerabilities, and cyber related news from the last week.
Top Cyber Stories of the Last Week
Cyber Attacks On The Rise For Businesses, Pushing Many To The Brink
The proportion of businesses targeted by cyber criminals in the past year increased from 38% to 43%, with over a quarter of those targeted (28%) experiencing five attacks or more. Those attacks are pushing many firms to the brink, with one in six businesses attacked (17%) saying the financial impact materially threatened the company’s future. On a more positive note, the report shows firms are responding to the cyber challenge: mean spending per business on cyber security has more than doubled in the last two years.
https://www.insurancejournal.com/news/international/2021/04/19/610514.htm
MI5 Warns Of Spies Using Linkedin To Trick Staff Into Spilling Secrets
At least 10,000 UK nationals have been approached by fake profiles linked to hostile states, on the professional social network LinkedIn, over the past five years, according to MI5. It warned users who had accepted such connection requests might have then been lured into sharing secrets. A campaign has been launched to educate government workers about the threat. The 10,000-plus figure includes staff in virtually every government departments as well as key industries, who might be offered speaking or business and travel opportunities that could lead to attempts to recruit them to provide confidential information.
https://www.bbc.co.uk/news/technology-56812746
SonicWall Warns Customers To Patch 3 Zero-Days Exploited In The Wild
Security hardware manufacturer SonicWall is urging customers to patch a set of three zero-day vulnerabilities affecting both its on-premises and hosted Email Security products. "In at least one known case, these vulnerabilities have been observed to be exploited 'in the wild,'" SonicWall said in a security advisory published earlier today. The company said it is "imperative" that organisations using its Email Security hardware appliances, virtual appliances, or software installations on Microsoft Windows Server machines immediately upgrade to a patched version.
The FBI Removed Hacker Backdoors From Vulnerable Microsoft Exchange Servers. Not Everyone Likes The Idea
The FBI had worked to remove malicious web shells from hundreds of computers in the United States that were running vulnerable versions of Microsoft Exchange Server. While the move will have helped keep many organisations secure, it has also raised questions about the direction of cyber security. Earlier this year, four zero-day vulnerabilities in Microsoft Exchange Server, which were being actively exploited by a nation-state-backed hacking operation, were uncovered. Microsoft released a critical security update to protect Exchange Server customers from cyber attacks exploiting the vulnerabilities in March, but a significant number of organisations have yet to apply the security patch.
Pulse Secure VPN Zero-Day Used To Hack Defense Firms, Govt Organisations
A zero-day authentication bypass vulnerability in the Pulse Connect Secure (PCS) SSL VPN appliance actively exploited in attacks against worldwide organisations and focused on US Defence Industrial base networks. As a workaround, the vulnerability can be mitigated on some gateways by disabling Windows File Share Browser and Pulse Secure Collaboration features using instructions available in the security advisory published earlier today.
SolarWinds Hack Could Cost Cyber Insurance Firms $90 Million
Cyber insurance vendors are expected to spend $90 million on incident response and forensic services for clients who were compromised by the SolarWinds hackers. “Although the SolarWinds attack is a cyber catastrophe from a national security perspective, insurers may have narrowly avoided a catastrophic financial incident to their businesses,” The Russian hackers behind the SolarWinds attack appear to have avoided large scale exploitation of victims, instead opting to maintain access and collect sensitive data. But if the SolarWinds hackers had been focused on interrupting business and destroying networks, the campaign could have been catastrophic for insurers.
https://www.crn.com/news/security/solarwinds-hack-could-cost-cyber-insurance-firms-90-million
Mount Locker Ransomware Aggressively Changes Up Tactics
The Mount Locker ransomware has shaken things up in recent campaigns with more sophisticated scripting and anti-prevention features, according to researchers. And, the change in tactics appears to coincide with a rebranding for the malware into “AstroLocker.” According to researchers, Mount Locker has been a swiftly moving threat. Having just hit the ransomware-as-a-service scene in the second half of 2020, the group released a major update in November that broadened its targeting capabilities (including searching for file extensions utilized by TurboTax tax-return software to encrypt). It also added improved detection evasion. Attacks have continued to escalate, and now, another major update signals “an aggressive shift in Mount Locker’s tactics,”.
https://threatpost.com/mount-locker-ransomware-changes-tactics/165559/
QR Codes Offer Easy Cyber Attack Avenues as Usage Spikes
The use of mobile quick-response (QR) codes in daily life, for both work and personal use, continues to rise – and yet, most people are not aware that these handy mobile shortcuts can open them up to savvy cyber attacks. A survey of 4,157 consumers across China, France, Germany, Japan, the U.K. and the U.S. It found that 57 percent of respondents have increased their QR code usage since mid-March 2020, mainly because of the need for touchless transactions in the wake of COVID-19. In all, three-quarters of respondents (77 percent) said they have scanned a QR code before, with 43 percent having scanned a QR code in the past week.
https://threatpost.com/qr-codes-cyberattack-usage-spikes/165526/
Google Alerts Continues To Be A Hotbed Of Scams And Malware
Google Alerts continues to be a hotbed of scams and malware that threat actors are increasingly abusing to promote malicious websites. While Google Alerts has been abused for a long time, a significant increase in activity over the past couple of weeks. People use Google Alerts to monitor for various terms related to cyber attacks, security incidents, malware, etc. In one Google Alert, almost every new article shared with people today by the service led to a scam or malicious website.
Threats
Ransomware
Campus Still Closed as Portsmouth University Reels from Suspected Ransomware
Ransomware Gang Tries To Extort Apple Hours Ahead Of Spring Loaded Event
Discord Nitro gift codes now demanded as ransomware payments
Phishing
Malware
IOT
Vulnerabilities
Google Issues Chrome Update Patching Seven Security Vulnerabilities
Zero-Day Vulnerabilities In Sonicwall Email Security Are Being Actively Exploited
Cisco Router Flaws Left Small Business Networks Open To Abuse
Firefox 88 Patches Bugs And Kills Off A Sneaky Javascript Tracking Trick
Data Breaches
Organised Crime & Criminal Actors
Cryptocurrency
Supply Chain
Nation State Actors
Denial of Service
Other News
As usual, contact us to help assess where your risks lie and to ensure you are doing all you can do to keep you and your business secure.
Look out for our weekly ‘Cyber Tip Tuesday’ video blog and on our YouTube channel.
You can also follow us on Facebook, Twitter and LinkedIn.
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
Black Arrow Cyber Threat Briefing 09 April 2021
Black Arrow Cyber Threat Briefing 09 April 2021: Ransomware Attacks Grew By 485% In 2020; Cyber Insurance Firm Suffers Cyber Attack; Ransom Gangs Emailing Victim Customers For Leverage; 'We Have Your Porn Collection' - The Rise Of Extortionware; Should Firms Be More Worried About Firmware Cyber Attacks; Armed Conflict Draws Closer As State-Backed Cyber Attacks Intensify; Coca-Cola Trade Secret Theft Underscores Importance Of Insider Threat Early Detection; Attackers Blowing Up Discord, Slack With Malware
Welcome to this week’s Black Arrow Cyber Threat Briefing – a weekly digest, collated and curated by our cyber experts to provide senior and middle management with an easy to digest round up of the most notable threats, vulnerabilities, and cyber related news from the last week.
Top Cyber Stories of the Last Week
Ransomware Attacks Grew By 485% In 2020
Ransomware attacks increased by an astonishing 485% in 2020 compared to 2019, according to Bitdefender’s 2020 Consumer Threat Landscape Report, which highlighted the ways cyber criminals targeted the COVID-19 pandemic. Interestingly, nearly two-thirds (64%) of the ransomware attacks took place in the first two quarters of 2020.
https://www.infosecurity-magazine.com/news/ransomware-attacks-grow-2020/
Cyber Insurance Firm Suffers Sophisticated Ransomware Cyber Attack; Data Obtained May Help Hackers Better Target Firm’s Customers
One of the largest insurance firms in the US CNA Financial was reportedly hit by a “sophisticated cyber security attack” on March 21, 2021. The cyber attack disrupted the company’s employee and customer services for three days as the company shut down “out of an abundance of caution” to prevent further compromise.
Ransom Gangs Emailing Victim Customers For Leverage
Some of the top ransomware gangs are deploying a new pressure tactic to push more victim organisations into paying an extortion demand: Emailing the victim’s customers and partners directly, warning that their data will be leaked to the dark web unless they can convince the victim firm to pay up.
https://krebsonsecurity.com/2021/04/ransom-gangs-emailing-victim-customers-for-leverage/
'We Have Your Porn Collection': The Rise Of Extortionware
Experts say the trend towards ransoming sensitive private information could affect companies not just operationally but through reputation damage. It comes as hackers bragged after discovering an IT Director's secret porn collection. The targeted US firm has not publicly acknowledged that it was hacked. In its darknet blog post about the hack last month, the cyber-criminal gang named the IT director whose work computer allegedly contained the files.
https://www.bbc.co.uk/news/technology-56570862
Should Firms Be More Worried About Firmware Cyber Attacks?
Microsoft recently put out a report claiming that businesses globally are neglecting a key aspect of their cyber security - the need to protect computers, servers, and other devices from firmware attacks. Its survey of 1,000 cyber security decision makers at enterprises across multiple industries in the UK, US, Germany, Japan, and China has revealed that 80% of firms have experienced at least one firmware attack in the past two years. Yet only 29% of security budgets have been allocated to protect firmware.
https://www.bbc.co.uk/news/business-56671419
Armed Conflict Draws Closer As State-Backed Cyber Attacks Intensify
The world is coming perilously close to nation states retaliating against cyber attacks with conventional weapons, according to a new HP report. Publicly available reports into state-sponsored attacks and interviews with scores of experts. It claimed there has been a 100% increase in “significant” state-backed attacks between 2017-20, and an average of over 10 publicly attributed attacks per month in 2020 alone.
https://www.infosecurity-magazine.com/news/armed-conflict-closer-state/
Coca-Cola Trade Secret Theft Underscores Importance Of Insider Threat Early Detection
The trial of Xiaorong You started in Greenville, TN, this week. She is accused of trade secret theft and economic espionage after allegedly stealing technologies owned by several companies, including her former employers Coca-Cola and Eastman Chemical Company. The value placed on the development of the stolen technologies is $119.6 million. Other affected companies include Azko-Nobel, Dow Chemical, PPG, TSI, Sherwin Williams and ToyoChem.
The details of the case suggest that the damages the accused is allegedly responsible for could have been minimized if better real-time insider threat detection methods had been in place. They also outline possible motives for the theft of the intellectual property: ego and money.
Attackers Blowing Up Discord, Slack With Malware
Workflow and collaboration tools like Slack and Discord have been infiltrated by threat actors, who are abusing their legitimate functions to evade security and deliver info-stealers, remote-access trojans (RATs) and other malware. The pandemic-induced shift to remote work drove business processes onto these collaboration platforms in 2020, and predictably, 2021 has ushered in a new level cyber criminal expertise in attacking them.
https://threatpost.com/attackers-discord-slack-malware/165295/
Scraped Data Of 500 Million LinkedIn Users Being Sold Online, 2 Million Records Leaked As Proof
An archive containing data purportedly scraped from 500 million LinkedIn profiles has been put for sale on a popular hacker forum, with another 2 million records leaked as a proof-of-concept sample by the post author. The four leaked files contain information about the LinkedIn users whose data has been allegedly scraped by the threat actor, including their full names, email addresses, phone numbers, workplace information, and more.
While users on the hacker forum can view the leaked samples for about $2 worth of forum credits, the threat actor appears to be auctioning the much-larger 500 million user database for at least a 4-digit sum, presumably in bitcoin.
Massive Facebook Data Breach Leaks Info On Millions Of Users
The personal information of hundreds of millions of Facebook users across the globe has been leaked online. Around 533 million Facebook users are thought to have been affected by the data breach, with phone numbers, Facebook ID, full name, location, past location, birthdate, email address, account creation date, relationship status, and personal bios all available. The data is thought to be the same set that was leaked in January 2021 and was available to purchase online, meaning Facebook has failed to secure its users once again.
https://www.techradar.com/uk/news/massive-facebook-data-breach-leaks-info-on-millions-of-users
Threats
Ransomware
Phishing
Malware
Mobile
IOT
Vulnerabilities
Critical Zoom vulnerability triggers remote code execution without user input
Bug allows attackers to hijack Windows time sync software used to track security incidents
AMD admits Zen 3 processors are vulnerable to Spectre-like side-channel attack
SAP Bugs Under Active Cyberattack, Causing Widespread Compromise
Data Breaches
Adult content from hundreds of OnlyFans creators leaked online
A huge trove of credit card records and Social Security numbers just got hacked
Booking.com fined €475,000 for late reporting of data breach
Nation State Actors
Privacy
Other News
Ubiquiti is accused of covering up a ‘catastrophic’ data breach — and it’s not denying it
VISA: Hackers increasingly using web shells to steal credit cards
Cloud-native watering hole attack: Simple and potentially devastating
As usual, contact us to help assess where your risks lie and to ensure you are doing all you can do to keep you and your business secure.
Look out for our weekly ‘Cyber Tip Tuesday’ video blog and on our YouTube channel.
You can also follow us on Facebook, Twitter and LinkedIn.
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
Black Arrow Cyber Threat Briefing 25 December 2020
Black Arrow Cyber Threat Briefing 25 December 2020: The Cyber Threat Is Real and Growing; Ransomware Attacks Surge in Q3; In 2021 there will be a cyber attack every 11 seconds; The West has suffered a massive cyber breach and it's hard to overstate how bad it is; Big tech companies including Intel, Nvidia, and Cisco were all infected during the SolarWinds hack
Welcome to this week’s Black Arrow Cyber Threat Briefing – a weekly digest, collated and curated by our cyber experts to provide senior and middle management with an easy to digest round up of the most notable threats, vulnerabilities and cyber related news from the last week.
Top Cyber Headlines of the Week
The Cyber Threat Is Real and Growing
The SolarWinds breach could be one of the most significant cyber incidents in history. Russian intelligence—likely the SVR, the foreign-intelligence branch—infiltrated and sat undetected on U.S. and other government networks for nearly 10 months. It was a sophisticated, smart and savvy attack that should alarm the public and private sectors.
We may not know the full extent of the damage for some time. Don’t be surprised if more government entities disclose that they too were victims of this attack. Don’t be surprised either if it emerges that private companies were hit. SolarWinds says it has more than 300,000 customers, including 400 companies in the Fortune 500. That’s a lot of potential victims.
https://www.wsj.com/articles/the-cyber-threat-is-real-and-growing-11608484291
Ransomware Attacks Surge in Q3 as Cyber Criminals Shift Tactics
A record growth in ransomware attacks took place in Q3 of 2020 compared to Q2, from 39% to 51% of all malware attempts according to a new study. The study also found that hacking accounted for 30% of all attacks during Q3, with cyber criminals reducing their emphasis on social engineering tactics compared with earlier this year. The researchers noted that the percentage of social engineering attacks using COVID-19 as a lure fell from 16% in Q2 to just 4% in Q3, which they attribute to people becoming more accustomed to this crisis. Additionally, social engineering attacks targeting organizations fell from 67% of all attempts in Q1 to under half (45%) in Q3.
https://www.infosecurity-magazine.com/news/ransomware-attacks-surge-q3/
In 2021, there will be a cyber attack every 11 seconds. Here’s how to protect yourself
Experienced outdoor athletes know that with winter rapidly approaching, the secret to success lies in protecting the core. That is, the body’s core temperature through layering, wicking and a host of ever-improving technical fabrics that prevent the cold, snow and ice from affecting performance. The same could be said for cyber security. With organizations and workers now in their ninth month of COVID-19, the time has come to prepare as the threat of cyber attacks becomes even more menacing.
The US, and much of the West, has suffered a massive cyber breach. It's hard to overstate how bad it is
Recent news articles have all been talking about the massive Russian cyber-attack against the United States, but that’s wrong on two accounts. It wasn’t a cyber-attack in international relations terms, it was espionage. And the victim wasn’t just the US, it was the entire world. But it was massive, and it is dangerous.
Espionage is internationally allowed in peacetime. The problem is that both espionage and cyber-attacks require the same computer and network intrusions, and the difference is only a few keystrokes. And since this Russian operation isn’t at all targeted, the entire world is at risk – and not just from Russia. Many countries carry out these sorts of operations, none more extensively than the US. The solution is to prioritize security and defense over espionage and attack.
https://www.theguardian.com/commentisfree/2020/dec/23/cyber-attack-us-security-protocols
Big tech companies including Intel, Nvidia, and Cisco were all infected during the SolarWinds hack
Last week, news broke that IT management company SolarWinds had been hacked, possibly by the Russian government, and the US Treasury, Commerce, State, Energy, and Homeland Security departments have been affected — two of which may have had emails stolen as a result of the hack. Other government agencies and many companies are investigating due to SolarWinds’ extensive client list. The Wall Street Journal is now reporting that some big tech companies have been infected, too.
Cisco, Intel, Nvidia, Belkin, and VMware have all had computers on their networks infected with the malware. There could be far more: SolarWinds had stated that “fewer than 18,000” companies were impacted, as if that number is supposed to be reassuring, and it even attempted to hide the list of clients who used the infected software. Today’s news takes some of SolarWinds’ big-name clients from “possibly affected’’ to “confirmed affected.”
https://www.theverge.com/2020/12/21/22194183/intel-nvidia-cisco-government-infected-solarwinds-hack
Researchers share the lists of victims of SolarWinds hack
Security experts started analyzing the DGA mechanism used by threat actors behind the SolarWinds hack to control the Sunburst/Solarigate backdoor and published the list of targeted organizations. Researchers from multiple cybersecurity firms published a list that contains major companies, including Cisco, Deloitte, Intel, Mediatek, and Nvidia. The researchers decoded the DGA algorithm used by the backdoor to assign a subdomain of the C2 for each of the compromised organizations.
https://securityaffairs.co/wordpress/112555/hacking/solarwinds-victims-lists.html
Threats
Ransomware
Ransomware: Attacks could be about to get even more dangerous and disruptive
IOT
New Critical Flaws in Treck TCP/IP Stack Affect Millions of IoT Devices
Malware
Emotet Returns to Hit 100K Mailboxes Per Day
Microsoft has discovered yet more SolarWinds malware
3 million users hit with infected Google Chrome and Microsoft Edge extensions
Vulnerabilities
Windows zero-day with bad patch gets new public exploit code
Script for detecting vulnerable TCP/IP stacks released
New SUPERNOVA backdoor found in SolarWinds cyberattack analysis
Smart Doorbell Disaster: Many Brands Vulnerable to Attack
Zero-day exploit used to hack iPhones of Al Jazeera employees
Signal: Cellebrite claimed to have 'cracked' chat app's encryption
Data Breaches
There's been a Nintendo Switch data leak, according to reports
Data breach hits 30,000 signed up to workplace pensions provider
Thousands of customer records exposed after serious data breach
Organised Crime
Cyber criminals have started indexing the dark web
Joker’s Stash Carding Site Taken Down
International sting shuts down 'favourite' VPN of cyber criminals
Dark Web Pricing Skyrockets for Microsoft RDP Servers, Payment-Card Data
NSA Warns of Hacking Tactics That Target Cloud Resources
Denial of Service
Cloudflare has identified a new type of DDoS attack inspired by an acoustic beat
Privacy
The pandemic has taken surveillance of workers to the next level
Other News
Dozens of Al Jazeera journalists allegedly hacked using Israeli firm's spyware
As usual, contact us to help assess where your risks lie and to ensure you are doing all you can do to keep you and your business secure.
Look out for our weekly ‘Cyber Tip Tuesday’ video blog and on our YouTube channel.
You can also follow us on Facebook, Twitter and LinkedIn.
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
Black Arrow Cyber Threat Briefing 13 November 2020
Black Arrow Cyber Threat Briefing 13 November 2020
Welcome to this week’s Black Arrow Cyber Threat Briefing – a weekly digest, collated and curated by our cyber experts to provide senior and middle management with an easy to digest round up of the most notable threats, vulnerabilities and cyber related news from the last week.
Top Cyber Headlines of the Week
Five Emerging Cyber-Threats to Watch Out for in 2021
What was the driving force behind your company’s digital strategy in 2020? Was it your CEO? Probably not. Your CTO or CISO? Perhaps.
For most organisations, it was COVID-19. In 2019, one company after another said: “work-from-home isn’t an option for us” or “we aren’t interested in shifting operations to the cloud.”
Then everything changed. The pandemic drove a massive shift towards remote work. For many companies, this wasn’t even an option — it was a case of ‘do or die.’
By April 2020, almost half of the American workforce was working from home. As organisations and employees become more comfortable with this, we shouldn’t expect a full return to the traditional in-office model anytime soon, if ever. Work-from-anywhere is the new way of doing business, with employees accessing cloud services, collaborative tools and remote systems from home and public networks – and not always through the safety of a VPN.
https://www.infosecurity-magazine.com/blogs/five-cyber-threats-2021/
Guernsey law firm fined £10,000 for data security breach
Trinity Chambers LLP sent private details about an individual and their family via emails and post, the Data Protection Authority (ODPA) found.
It said a lack of security had given "unconnected" third parties access to the data.
The breach of data by Trinity was the result of "repeated human error", an investigation found.
https://www.bbc.co.uk/news/world-europe-guernsey-54854333
Every employee has a cyber security blind spot
80% of companies say that an increased cyber security risk caused by human factors has posed a challenge during the COVID-19 pandemic, particularly in times of heightened stress.
This is a new report that explores the role employees and their personality play in keeping organisations safe from cyber threats. Including that:
· Cyber crime has increased by 63% since the COVID-19 lockdown was introduced
· Human error has been the biggest cyber security challenge during the COVID-19 pandemic, according to CISOs
· Just a quarter of businesses consider their remote working strategy effective
· 47% of people are concerned about their ability to manage stress during the coronavirus crisis
https://www.helpnetsecurity.com/2020/11/09/cybersecurity-blind-spot/
Zoom settles FTC charges for misleading users about security features
Video conferencing software maker Zoom has reached a deal today with the US Federal Trade Commission to settle accusations that its misled users about some of its security features.
During the height of the COVID-19 pandemic, Zoom had attracted users to its platform with misleading claims that its product supported "end-to-end, 256-bit encryption" and that its service would store recorded calls in an encrypted format.
However, in a complaint filed earlier this year, the investigators found that Zoom's claims were deceptive.
Despite claiming to support end-to-end encrypted (E2EE) calls, Zoom didn't support E2EE calls in the classic meaning of the word.
https://www.zdnet.com/article/zoom-settles-ftc-charges-for-misleading-users-about-security-features/
Threats
Ransomware
How Ryuk Ransomware operators made $34 million from one victim
One hacker group that is targeting high-revenue companies with Ryuk ransomware received $34 million from one victim in exchange for the decryption key that unlocked their computers.
The threat actor is highly proficient at moving laterally inside a compromised network and erasing as much of their tracks as possible before detonating Ryuk ransomware.
Ransomware hits e-commerce platform X-Cart
E-commerce software vendor X-Cart suffered a ransomware attack at the end of October that brought down customer stores hosted on the company's hosting platform.
The incident is believed to have taken place after attackers exploited a vulnerability in a third-party software to gain access to X-Cart's store hosting systems.
https://www.zdnet.com/article/ransomware-hits-e-commerce-platform-x-cart
Linux version of RansomEXX ransomware discovered
A Linux version of the RansomEXX ransomware, marking the first time a major Windows ransomware strain has been ported to Linux to aid in targeted intrusions.
RansomEXX is a relatively new ransomware strain that was first spotted earlier this year in June.
https://www.zdnet.com/article/linux-version-of-ransomexx-ransomware-discovered/
Laptop mega-manufacturer Compal hit by DoppelPaymer ransomware – same one that hit German hospital
Compal, the world’s second-largest white-label laptop manufacturer, has been hit by the file-scrambling DoppelPaymer ransomware gang – and the hackers want $17m in cryptocurrency before they'll hand over the decryption key.
The Taiwanese factory giant, which builds systems for Apple, Lenovo, Dell, and HP, finally admitted malware infected its computers and encrypted its documents after first insisting it had suffered no more than an IT "abnormality" and that its staff had beaten off a cyber-attack.
https://www.theregister.com/2020/11/09/compal_ransomware_report/
Capcom hit by ransomware attack, is reportedly being extorted for $11 million
Earlier this week it emerged that third-party giant Capcom's internal systems had been hacked, though the company claimed that no customer data was affected.
It has now emerged that the publisher was targeted by the Ragnar Locker ransomware, software designed to exfiltrate information from internal networks before encrypting the lot: at which point the victim is locked-out, contacted, and extorted.
Business Email Compromise (BEC)
Jersey business targeted in £130,000 invoice scam
A Jersey building company has been targeted by a sophisticated impersonation scam, which saw fraudsters intercept more than £130,000 in invoice payments.
The owners, who wish to remain anonymous, said they were "left reeling" after realising their email correspondence with a customer had been hacked, and payments diverted to a scam bank account.
After taking swift action, they were able to recover all their money, but they now want to make sure other islanders do not fall victim. They are encouraging businesses in particular to be "extra vigilant".
https://www.itv.com/news/channel/2020-11-13/jersey-business-targeted-in-130000-invoice-scam
Phishing
Smishing attack tells you “mobile payment problem” – don’t fall for it!
As we’ve warned before, phishing via SMS, or smishing for short, is still popular with cybercriminals.
Sure, old-fashioned text messages have fallen out of favour for personal communications, superseded round the world by instant messaging apps such as WhatsApp, WeChat, Instagram, Telegram and Signal.
But for brief, one-off business communications such as “Your home delivery will arrive at 11:30 today” or “Your one-time login code is 217828”, SMS is still a popular and useful messaging system.
That’s because pretty much every mobile phone in the world can receive text messages, regardless of its age, feature set or ability to access the internet.
Even if you’ve got no credit to send messages or make calls, no third-party apps installed, and no Wi-Fi connectivity, SMSes sent to you will still show up.
Malware
Play Store identified as main distribution vector for most Android malware
The official Google Play Store has been identified as the primary source of malware installs on Android devices in a recent academic study — considered the largest one of its kind carried out to date.
Using telemetry data, researchers analysed the origin of app installations on more than 12 million Android devices for a four-month period between June and September 2019.
In total, researchers looked at more than 34 million APK (Android application) installs for 7.9 million unique apps.
This new malware wants to add your Linux servers and IoT devices to its botnet
A new form of malware is targeting Linux servers and Internet of Things (IoT) devices and adding them to a botnet in what appears to be the first stage of a hacking campaign targeting cloud-computing infrastructure – although the purpose of the attacks remains unclear.
The malicious worm has been dubbed Gitpaste-12, reflecting on how it uses GitHub and Pastebin for housing component code and has 12 different means of compromising Linux-based x86 servers, as well as Linux ARM- and MIPS-based IoT devices.
New 'Ghimob' malware can spy on 153 Android mobile applications
Security researchers have discovered a new Android banking trojan that can spy and steal data from 153 Android applications.
Named Ghimob, the trojan is believed to have been developed by the same group behind the Astaroth (Guildma) Windows malware, according to a report published.
Distribution was never carried out via the official Play Store.
Instead, the Ghimob group used emails or malicious sites to redirect users to websites promoting Android apps.
https://www.zdnet.com/article/new-ghimob-malware-can-spy-on-153-android-mobile-applications/
Microsoft Teams Users Under Attack in ‘Fake Updates’ Malware Campaign
Attackers are using ads for fake Microsoft Teams updates to deploy backdoors, which use Cobalt Strike to infect companies’ networks with malware.
The campaign is targeting various types of companies, with recent targets in the K-12 education sector, where organisations are currently dependent on using apps like Teams for videoconferencing due to COVID-19 restrictions.
Cobalt Strike is a commodity attack-simulation tool that’s used by attackers to spread malware, particularly ransomware. Recently, threat actors were seen using Cobalt Strike in attacks exploiting Zerologon, a privilege-elevation flaw that allows attackers to access a domain controller and completely compromise all Active Directory identity services.
https://threatpost.com/microsoft-teams-fakeupdates-malware/161071/
DDoS
DDoS attacks are cheaper and easier to carry out than ever before
DDoS attacks are getting more complex and more sophisticated while also getting cheaper and easier to carry out as cyber criminals take advantage of the sheer number of insecure internet-connected devices.
Distributed Denial of Service attacks have been a problem for many years, with cyber attackers gaining control of armies of devices and directing their internet traffic at targets in order to take the victim offline.
The disruption causes problems for both businesses and individual users who are prevented from accessing digital services they require – and that's especially a problem as 2020's coronavirus pandemic has forced people to be more reliant on digital services than ever before.
https://www.zdnet.com/article/ddos-attacks-are-cheaper-and-easier-to-carry-out-than-ever-before/
IoT
IoT security is a mess. These guidelines could help fix that
The supply chain around the Internet of Things (IoT) has become the weak link in cyber security, potentially leaving organisations open to cyber attacks via vulnerabilities they're not aware of. But a newly released set of guidelines aims to ensure that security forms part of the entire lifespan of IoT product development.
The Guidelines for Securing the IoT – Secure Supply Chain for IoT report from the European Union Agency for Cybersecurity (ENISA) sets out recommendations throughout the entire IoT supply chain to help keep organisations protected from vulnerabilities that can arise when building connected things.
https://www.zdnet.com/article/iot-security-is-a-mess-these-guidelines-could-help-fix-that/
Vulnerabilities
Windows 10 update created a major password problem
A temporary fix for a frustrating Windows 10 bug that prevents software from storing account credentials, meaning the user must re-enter their username and password each time they log-in.
The flaw is also said to delete cookies held in web browsers, preventing websites from memorising credentials and serving bespoke content to the user.
First reported in April, the issue is present in specific builds of Windows 10 version 2004 and affects applications such as Outlook, Chrome, Edge, OneDrive and more.
https://www.techradar.com/news/windows-10-update-made-a-right-mess-of-this-basic-password-feature
Colossal Intel Update Anchored by Critical Privilege-Escalation Bugs
A massive Intel security update this month addresses flaws across a myriad of products – most notably, critical bugs that can be exploited by unauthenticated cyber criminals in order to gain escalated privileges.
These critical flaws exist in products related to Wireless Bluetooth – including various Intel Wi-Fi modules and wireless network adapters – as well as in its remote out-of-band management tool, Active Management Technology (AMT).
Overall, Intel released 40 security advisories on Tuesday, each addressing critical-, high- and medium-severity vulnerabilities across various products. That by far trumps October’s Intel security update, which resolved one high-severity flaw.
https://threatpost.com/intel-update-critical-privilege-escalation-bugs/161087/
Hackers are exploiting unpatched VoIP flaws to compromise business accounts
A hacking campaign has compromised VoIP (Voice over Internet Protocol) phone systems at over 1,000 companies around the world over the past year in a campaign designed to make profit from selling compromised accounts.
While the main purpose appears to be dialling premium rate numbers owned by attackers or selling phone numbers and call plans that others can use for free, access to VoIP systems could provide cyber criminals with the ability to conduct other attacks, including listening to private calls, cryptomining, or even using compromised systems as a steppingstone towards much more intrusive campaigns.
One hacking group has compromised the VoIP networks of almost 1,200 organisations in over 20 countries by exploiting the vulnerability, with over half the victims in the UK. Industries including government, military, insurance, finance and manufacturing are believed to have fallen victim to the campaign
Google patches two more Chrome zero-days
Google has released today Chrome version 86.0.4240.198 to patch two zero-day vulnerabilities that were exploited in the wild.
These two bugs mark the fourth and fifth zero-days that Google has patched in Chrome over the past three weeks.
The difference this time is that while the first three zero-days were discovered internally by Google security researchers, these two new zero-days came to Google's attention after tips from anonymous sources.
https://www.zdnet.com/article/google-patches-two-more-chrome-zero-days/
Data Breaches
Ticketmaster fined £1.25m over payment data breach
Ticketmaster UK has been fined £1.25m for failing to keep its customers' personal data secure.
The fine was issued by the Information Commissioner's Office (ICO) following a cyber-attack on the Ticketmaster website in 2018.
The ICO said personal information and payment details had potentially been stolen from more than nine million customers in Europe.
https://www.bbc.co.uk/news/technology-54931873
Millions of Hotel Guests Worldwide Caught Up in Mass Data Leak
A cloud misconfiguration affecting users of a popular reservation platform threatens travellers with identity theft, scams, credit-card fraud and vacation-stealing.
A widely used hotel reservation platform has exposed 10 million files related to guests at various hotels around the world, thanks to a misconfigured Amazon Web Services S3 bucket. The records include sensitive data, including credit-card details.
Prestige Software’s “Cloud Hospitality” is used by hotels to integrate their reservation systems with online booking websites like Expedia and Booking.com.
https://threatpost.com/millions-hotel-guests-worldwide-data-leak/161044/
DWP exposed 6,000 people’s data online for two years
The Department for Work and Pensions (DWP) has removed the personal details of thousands of people after they were exposed online for two years.
The files, published in March and June 2018, listed routine payments to the outsourcing giant Capita and included the National Insurance (NI) numbers of approximately 6,000 people, according to the Mirror. These individuals were believed to be applying for the disability benefit, PIP. No other personal data was exposed in the incident.
https://www.itpro.co.uk/security/data-breaches/357724/dwp-data-breach-exposed-6000-ni-numbers
Data breach at Mashable leaks users’ personal information online
Technology and culture news website Mashable have announced that the personal data of users has been discovered in a leaked database posted on the internet.
In a statement issued this week, Mashable confirmed that a database containing information from readers who made use of the platform’s social media sign-in feature had been found online.
The media company said that “a hacker known for targeting websites and apps” was responsible for the breach. The suspect has not been named.
Leaked data is said to include the full names, locations, email addresses, genders, IP addresses, and links to social media profiles of users.
Other News
Try to avoid thinking of the internet as a flashy new battlefield, warns former NCSC chief
https://www.theregister.com/2020/11/11/ciaran_martin_speech_cyber_policy/
Microsoft says three APTs have targeted seven COVID-19 vaccine makers
https://www.zdnet.com/article/microsoft-says-three-apts-have-targeted-seven-covid-19-vaccine-makers/
New stealthy hacker-for-hire group mimics state-backed attackers
As usual, contact us to help assess where your risks lie and to ensure you are doing all you can do to keep you and your business secure.
Look out for our weekly ‘Cyber Tip Tuesday’ video blog and on our YouTube channel.
You can also follow us on Facebook, Twitter and LinkedIn.
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
Key InfoSec Terms and Concepts Explained: Vulnerabilities, Threats, Risks and Countermeasures - Cyber Tip Tuesday Explainer Series
Key InfoSec Terms and Concepts Explained: Vulnerabilities, Threats, Risks and Countermeasures - Cyber Tip Tuesday Explainer Series
Key InfoSec Terms and Concepts Explained: Vulnerabilities, Threats, Risks and Countermeasures - Cyber Tip Tuesday Explainer Series
Cyber Threat Briefing 16 October 2020: ransomware tidal wave; notable ransomware victims from the last week; BEC Attacks: Nigeria no longer epicentre, losses top $26B; Trickbot back; MS fix 87 vulns
Cyber Threat Briefing 16 October 2020: ransomware tidal wave of attacks; Notable ransomware victims of the last week; BEC Attacks: Nigeria No Longer the Epicentre as Losses top $26B; Trickbot back after disruption attempts; Microsoft October 2020 Patch Tuesday fixes 87 vulnerabilities; Malware gangs love open source offensive hacking tools
Welcome to this week’s Black Arrow Cyber Threat Briefing – a weekly digest, collated and curated by our cyber experts to provide senior and middle management with an easy to digest round up of the most notable threats, vulnerabilities and cyber related news from the last week.
Threats
Ransomware
Ransomware is growing and growing and getting worse all the time, with the G7 this week warning of ‘a tidal wave of ransomware attacks’ [source]. It is fast approaching becoming such a problem that it may soon reach epidemic status with few organisations left unaffected as firm after firm falls victim.
The ransomware gangs have turned crime into a multi-million pound business empire, it is estimated that $7.5 billion was extorted from victims last year in the United States alone [source], putting any legitimate industry or business sector to shame in term of meteoric growth. This is not small scale actors working out of their bedrooms, they have customer support centres and 24/7 helplines, they have plush offices and flash cars, paid for by the victims of their crimes, paid for by firms like yours paying ransoms.
And here's how attackers are getting in: in nearly half (47%) of ransomware cases gangs used the open remote desktop protocol, a tool that has been used by many companies to help staff work from home, but which can also give attackers a way in if it is not correctly secured.
More than a quarter (26%) of cases were traced back to a phishing email, and a smaller number used specific vulnerability exploits (17%), including Citrix NetScaler CVE-2019-19781 and Pulse VPN CVE-2019-11510. This was followed by account takeovers, at 10%. [source]
Criminal gangs have earned so much money and power they are now outsourcing much of the labour, allowing them to live of their spoils while their empires continue to grow, while they do next to nothing, with more and more joining their ranks [source]
As long as even a small number of victims pay the ransom this remains highly lucrative for attackers.
The ransom for Software AG is $23m, but they will demand much smaller sums from much smaller firms – so how are they doing this? Are larger firms being specifically targeted with tailored phishing campaigns, where they hope they will get lucky in getting an employee to fall for the bait, where lower value targets are being hit with machine/algorithmic generated phishing attacks, with lower levels of sophistication and more of a ‘spray and pray’ approach, hoping casting a wide enough net will still result in larger numbers of lower value victims.
We keep trying to warn firms how bad this is getting, and we don’t do this to drum up business, we do this because we are hugely concerned about the direction this is going and how damaging this can be for any firm.
Many firms are reluctant to take cyber security seriously, believing it won’t happen to them, but it is happening to firm after firm after firm who believed it wouldn’t happen to them. It’s too late to start thinking about what you should have done after you’ve become a victim, it’s far better, and far cheaper, to take steps to avoid being a victim in the first place than trying to recover or pay the ransom.
Of the increasing number of firms that do go hit, many don’t survive, and those that do often find things are never the same again, with impacts on confidence levels in your staff and in your IT and information security departments [source]
Ransomware is not only affecting desktops, laptops and servers, but also now increasingly Android and other mobile platforms [source]
Protecting against ransomware is not a luxury or something that can kicked down the road to look at another day, firms need to ensure they are protecting themselves against this threat now – before they become a victim.
Notable ransomware victims of the last week
There have been a number of high profile victims of ransomware in the last week, notably Software AG, a German conglomerate with operations in more than 70 countries, which was attacked by the Clop group who are threatening to dump stolen data if the $23 million ransom is not paid.
Carnival Cruises were hit with ransomware affecting data and personal information for guests, employees and crew for Carnival Cruises, Holland America and Seabourn as well as casino operations.
Early indications point to the disruption being experiences by Hackney Council with their systems stemming from a ransomware attack, although this has not been confirmed.
BEC
BEC Attacks: Nigeria No Longer the Epicentre as Losses top $26B
Business Email Compromise (BEC) Fraudsters now have bases of operation across at least 39 countries and are responsible for $26 billion in losses annually, and growing.
A study of more than 9,000 instances of BEC attacks all over the world shows that the number has skyrocketed over the past year, and that the social-engineering scam has expanded well beyond its historic roots in Nigeria.
Why this matters:
A recent report entitled The Global Reach of Business Email Compromise, found that these attacks cost businesses a staggering $26 billion every year. And that trend appears to be accelerating. In fact, researchers found BEC attacks currently make up a full 40 percent of cyber crime losses globally, impacting at least 177 countries.
For context, the Anti-Phishing Working Group recently find that the average wire transfer in a BEC scan is around $80,000.
In a BEC attack, a scammer impersonates a company executive or other trusted party and tries to trick an employee responsible for payments or other financial transactions into writing money to a bogus account. Attackers usually conduct a fair amount of recon work, studying executive styles and uncovering the organisations vendors, billing system practices and other information to help mount a convincing attack.
Read more: https://threatpost.com/bec-attacks-nigeria-losses-snowball/160118/
Trickbot back after disruption attempts
The Trickbot botnet looks to be working once again, despite separate efforts in the past few weeks aimed at disrupting its operation.
Earlier this month the Emotet spam botnet – which is often the precursor to TrickBot being loaded onto a system – began receiving spam templates intended for mass distribution. These spam templates contained Microsoft Word document attachments with malicious macros that fetch and load a copy of Emotet onto the victim machine. The Emotet bot reached out to its controllers and received commands to download and execute Trickbot on victim machines.
The Trickbot group tag that researchers identified is tied to a typical infection campaign that information security researchers have been observing for the past 6 months or more.
Additionally, Intel 471 researchers saw an update to the Trickbot plugin server configuration file. Fifteen server addresses were added, and two old servers were retained in the configuration, along with the server’s ‘.onion’ address. This was likely done as a fix that would help operators maintain that their infrastructure remains operational. [link]
Why this matters:
The fix is another round in the back-and-forth between Trickbot’s operators and the separate public and private sector parties that have attempted to disrupt the botnet’s actions. This includes actions by the US Cyber Command and Microsoft, who issued a public statement that it had taken legal action to “combat ransomware ahead of U.S. elections.” The legal action involved Microsoft attempting to disrupt a number of Trickbot command and control server IP addresses in the United States.
The fact that Trickbot has resumed normal operations despite the best efforts of the likes of the US Cyber Command and Microsoft shows how resilient of an operation Trickbot is, and how much more effort is needed to fully take the botnet offline for good. The botnet’s operators have all the IT support of legitimate enterprises – continuity planning, backups, automated deployment, and a dedicated workforce – that allow them to quickly react to disruptive measures.
Read more: https://public.intel471.com/blog/trickbot-online-emotet-microsoft-cyber-command-disruption-attempts/
Vulnerabilities
Microsoft October 2020 Patch Tuesday fixes 87 vulnerabilities
Microsoft this week released its monthly batch of security updates known as Patch Tuesday, and this month the OS maker has patched 87 vulnerabilities across a wide range Microsoft products.
By far, the most dangerous bug patched this month is CVE-2020-16898. Described as a remote code execution (RCE) vulnerability in the Windows TCP/IP stack, this bug can allow attackers to take over Windows systems by sending malicious ICMPv6 Router Advertisement packets to an unpatched computer via a network connection.
Another bug to keep an eye on is CVE-2020-16947, a remote code execution issue in Outlook. Microsoft says this bug can be exploited by tricking a user to open a specially crafted file with an affected version of Microsoft Outlook software. [source1] [source2]
Why this matters:
The bug was discovered internally by Microsoft engineers, and OS versions vulnerable to CVE-2020-16898 include Windows 10 and Windows Server 2019.
With a severity score of 9.8 out of a maximum 10, Microsoft considers the bug dangerous and likely to be weaponised, and rightfully so.
Patching the bug is recommended, but workarounds such as disabling ICMPv6 RDNSS support also exist, which would allow system administrators to deploy temporary mitigations until they quality-test this month’s security updates for any OS-crashing bugs.
Critical SonicWall VPN Portal Bug Allows DoS, Worming RCE
A critical security bug in the SonicWall VPN Portal can be used to crash the device and prevent users from connecting to corporate resources. It could also open the door to remote code execution (RCE), researchers said.
The flaw (CVE-2020-5135) is a stack-based buffer overflow in the SonicWall Network Security Applicance (NSA). According to researchers who discovered it, the flaw exists within HTTP/HTTPS service used for product management and SSL VPN remote access. [source]
Why this matters:
An unskilled attacker could trigger a persistent denial-of-service condition using an unauthenticated HTTP request involving a custom protocol handler.
Adding insult to injury, this particular flaw exists in a pre-authentication routine, and within a component (SSL VPN) which is typically exposed to the public internet.
‘More Than A Billion’ Phone Wide Open To ‘Backdoor’ Remote Code Execution in Adtech Company’s Code
Malicious code impacting more than a billion smartphone owners is currently in the wild and enabling remote code execution. [source]
Why this matters:
Remote code execution is a very serious security violation, and basically enables the owner of that code do almost anything they want on your phone.
Miscellaneous Cyber News of the Weeks
Malware gangs love open source offensive hacking tools
In the cyber security field, the term OST (Open Source Tools) refers to software apps, libraries, and exploits that possess offensive hacking capabilities and have been released as either free downloads or under an open source license.
OST projects are usually released to provide a proof-of-concept exploit for a new vulnerability, to demonstrate a new (or old) hacking technique, or as penetration testing utilities shared with the community.
These discussions have been taking place for more than a decade. However, they have always been based on personal experiences and convictions, and never on actual raw data.
That changed this week when a security researcher compiled data on 129 open source offensive hacking tools and searched through malware samples and cyber-security reports to discover how widespread was the adoption of OST projects among hacking groups — such as low-level malware gangs, elite financial crime groups, and even nation-state sponsored APTs. [source]
The results were compiled in an interactive map – available here
Why this matters:
Today, OST is one of the most (if not the most) controversial topics in the information security community.
On one side, you have the people who are in favour of releasing such tools, arguing that they can help defenders learn and prepare systems and networks for future attacks.
On the opposing side, you have the ones who say that OST projects help attackers reduce the costs of developing their own tools and hiding activities into a cloud of tests and legitimate pen-tests.
Fitbit Spyware Steals Personal Data via Watch Face
A researcher has found they can take advantage of lax Fitbit privacy controls to build a malicious spyware watch face.
A wide-open app-building API (Application Programming Interface) could allow an attacker to build a malicious application that could access Fitbit user data, and send it to any server.
A proof-of-concept was created to do just that, after realizing that Fitbit devices are loaded with sensitive personal data. [source]
Why this matters:
Essentially, the API could send device type, location and user information including gender, age, height, heart rate and weight and it could also access calendar information. While this doesn’t include PII profile data, the calendar invites could expose additional information such as names and locations.
The researcher was able to make the app available through the Fitbit Gallery (where Fitbit showcases various third-party and in-house apps). Thus, the spyware appears legitimate, and increase the likelihood it would be downloaded.
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
As usual, contact us to help assess where your risks lie and to ensure you are doing all you can do to keep you and your business secure.
Look out for our weekly ‘Cyber Tip Tuesday’ video blog and on our YouTube channel.
Cyber Weekly Flash Briefing 25 September 2020: GFSC consult on new Cyber Rules; FinCEN leak exposes poor data security; Zerologon attacks detected; ransomware gang behind German hospital death
Cyber Weekly Flash Briefing 25 September 2020: GFSC consulting on new Cyber Rules; Leaked FinCEN files expose poor data security; Microsoft detects active Zerologon attacks; ransomware crew fingered for German hospital death; malware that steals your most sensitive data on the rise; Ransomware is evolving; top threats inside malicious emails; Credential Stuffing behind Recent Attacks
Links to articles are for interest and awareness and linking to or reposting external content does not endorse any service or product, likewise we are not responsible for the security of external links.
GFSC new Cyber Rules and Guidance out for consultation
The GFSC have put the Cyber Security Rules and Guidance Consultation Paper up on their website and consultation hub.
Why this matters:
The new rules and accompanying guidance came out of the 18 month thematic review which ended last year, which found that regulated financial service firms within the Bailiwick of Guernsey were not taking risks from cyber threats seriously enough and were lacking in appropriate protections and controls. These new rules seek to rectify this but many firms on the Island are going to have to do work to become compliant, especially around their ability to monitor for and detect unusual activity that could be indicative of a actual or attempted intrusion or breach.
The rules and guidance can be found here:
Leaked FinCEN files expose poor data security
Leaked documents, dubbed the “FinCEN Files,” describe global money laundering of $2 trillion processed by many of the world’s biggest banks between 2000 and 2017. The reveal illuminates the struggle for the financial industry and government to provide ironclad data protection.
“This sensational and unprecedented leak clearly demonstrates a wide spectrum of data protection weaknesses in the governmental sector, affecting even the most developed Western countries,” Ilia Kolochenko, founder and CEO of ImmuniWeb, said of the files.
“From a cybersecurity standpoint, we may expect a growing lack of trust to governmental agencies, which on one side have quasi-unlimited access to the most sensitive data of the largest organisations, while cannot duly safeguard this data on the other side,” he said.
The latest disclosure exposing apparently insufficient attempts by the public and private sectors to curb corruption came to light in a BuzzFeed News report which detailed more than 2,500 reported cases, including 2,100 Suspicious Activity Reports (SAR) filed by financial institutions with the U.S. Treasury Department’s Financial Crimes Enforcement Network (FinCEN).
JPMorgan Chase, Citigroup, Bank of America, Deutsche Bank, HSBC and Standard Chartered are among the financial institutions cited in the leaked files as processing dirty money around the world. The documents may have come from a whistleblower or insider at FinCEN. The International Consortium of Investigative Journalists (ICIJ), which represents 108 news organizations in 88 countries, is conducting a probe of the matter.
Why this matters:
Other similar investigative reports on similar wrongdoing focused single financial, tax or legal institutions, such as the 2017 Panama Papers emanating from clients of the law firm Mossack Fonseca. But the FinCEN docs reveal that a wide array of people from oligarchs and corrupt politicians to drug dealers and organised crime throughout the world know how to circumvent the system’s supposed checks and balances.
Read more: https://www.scmagazine.com/home/security-news/leaked-fincen-files-expose-poor-data-security/
Microsoft says it detected active attacks leveraging Zerologon vulnerability
Hackers are actively exploiting the Zerologon vulnerability in real-world attacks, Microsoft's security intelligence team said this week.
The attacks were expected to happen, according to security industry experts.
Multiple versions of weaponized proof-of-concept exploit code have been published online in freely downloadable form since details about the Zerologon vulnerability were revealed a week ago.
The first proof-of-concept exploit was published hours after the explanatory blog post, confirming initial analysis that the Zerologon bug is easy to exploit, even by low-skilled threat actors.
Why this matters:
Put simply the Zerologon bug is a vulnerability in Netlogon, the protocol used by Windows systems to authenticate against a Windows Server running as a domain controller. Exploiting the Zerologon bug can allow hackers to take over the domain controller, and inherently a company's internal network.
Zerologon was described by many as the most dangerous bug revealed this year. US federal agencies were given three days to patch domain controllers or disconnect them from federal networks.
As several security experts have recommended since Microsoft revealed the attacks, companies that have their domain controller exposed on the internet should take systems offline to patch them.
These internet-reachable servers are particularly vulnerable as attacks can be mounted directly, without the hacker first needing a foothold on internal systems.
Doppelpaymer ransomware crew fingered for attack on German hospital that caused death of a patient
The Doppelpaymer ransomware gang were behind the cyber-attack on a German hospital that led to one patient's death, according to local sources.
A German newspaper carried a report that Doppelpaymer's eponymous ransomware had been introduced to the University Hospital Düsseldorf's network through a vulnerable Citrix product.
That ransomware infection, activated last week, is said by local prosecutors to have led to the death of one patient who the hospital was unable to treat on arrival. She died in an ambulance while being transported to another medical facility with functioning systems.
Why this matters:
According to a report handed to the provincial government of North Rhine-Westphalia and seen by the German Press Association (DPA), the ransomware's loader had been lurking on the hospital's network since December 2019, the same month a patch was issued by Citrix for CVE-2019-19781 – the same vuln exploited to hit the hospital.
Whilst this is the first time a loss of life has been directly attributed to ransomware the threats are increasing all the time.
Vulnerabilities must be patched as soon as possible to stop known vulnerabilities from being used in attacks.
Read more: https://www.theregister.com/2020/09/23/doppelpaymer_german_hospital_ransomware/
“LokiBot,” the malware that steals your most sensitive data, is on the rise
Agencies in the US have reported seeing a big uptick in infections coming from LokiBot, an open source DIY malware package for Windows that’s openly sold or traded for free in underground forums. It steals passwords and cryptocurrency wallets, and it can also download and install new malware.
The increase was measured by an automated intrusion-detection system for collecting, correlating, analysing, and sharing computer security information.
US cyber agency CISA observed a notable increase in the use of LokiBot malware by malicious cyber actors since July 2020 according to an alert issued this week.
Why this matters:
While not quite as prevalent or noxious as the Emotet malware, LokiBot remains a serious and widespread menace. The infostealer spreads through a variety of methods, including malicious email attachments, exploitation of software vulnerabilities, and trojans sneaked into pirated or free apps. Its simple interface and reliable codebase make it attractive to a wide range of crooks, including those who are new to cybercrime and have few technical skills.
Ransomware is evolving, but the key to preventing attacks remains the same
Ransomware attacks are getting more aggressive according to a senior figure at Europe's law enforcement agency, but there are simple steps which organisations can follow to protect themselves – and their employees – from falling victim to attacks.
"Ransomware is one of the main threats," said the head of operations at Europol's European Cybercrime Centre (EC3). Europol supports the 27 EU member states in their fight against terrorism, cybercrime and other serious and organised forms of crime.
"Criminals behind ransomware attacks are adapting their attack vectors, they're more aggressive than in the past – they're not only encrypting the files, they're also exfiltrating data and making it available," he explained. "From a law enforcement perspective, we have been monitoring this evolution."
Why this matters:
This year has seen a rise in ransomware attacks where cyber criminals aren't just encrypting the networks of victims and demanding six-figure bitcoin payment to return the files, but they're also threatening to publish sensitive corporate information and other stolen data if the victim doesn't pay the ransom.
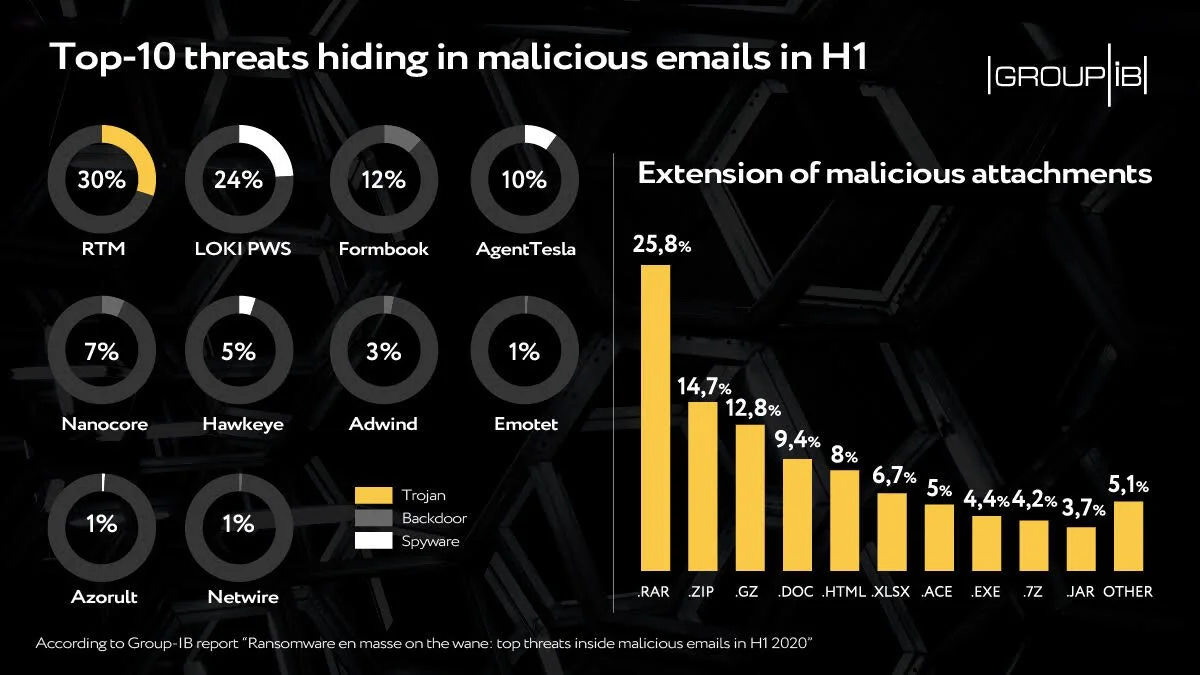
A look at the top threats inside malicious emails
Web-phishing targeting various online services almost doubled during the COVID-19 pandemic: it accounted for 46 percent of the total number of fake web pages, Group-IB reveals.
Ransomware, the headliner of the previous half-year, walked off stage: only 1 percent of emails analysed contained this kind of malware. Every third email, meanwhile, contained spyware, which is used by threat actors to steal payment data or other sensitive info to then put it on sale in the darknet or blackmail its owner.
Downloaders, intended for the installation of additional malware, and backdoors, granting cybercriminals remote access to victims’ computers, also made it to top-3. They are followed by banking Trojans, whose share in the total amount of malicious attachments showed growth for the first time in a while.
According to the data, in H1 2020 detected malicious emails were:
43 percent of the malicious mails had attachments with spyware or links leading to their downloading
17 percent contained downloaders
16 percent had backdoors
15 percent had banking trojans
Ransomware, which in the second half of 2019 hid in every second malicious email, almost disappeared from the mailboxes in the first six months of this year with a share of less than 1 percent.
Why this matters:
These findings confirm adversaries’ growing interest in Big Game Hunting. Ransomware operators have switched from attacks en masse on individuals to corporate networks. Thus, when attacking large companies, instead of infecting the computer of a separate individual immediately after the compromise, attackers use the infected machine to move laterally in the network, escalate the privileges in the system and distribute ransomware on as many hosts as possible.
Read more: https://www.helpnetsecurity.com/2020/09/21/top-threats-inside-malicious-emails/
Credential Stuffing: the Culprit of Recent Attacks
A year ago, researchers found that 2.2 billion leaked records, known as Collection 1-5, were being passed around by hackers. This ‘mega leak’ included 1.2 billion unique email addresses and password combinations, 773 million unique email addresses and 21 million plaintext passwords. With this treasure trove, hackers can simply test email and password combinations on different sites, hoping that a user has reused one. This popular technique is known as credential stuffing and is the culprit of many recent data breaches.
There are only a few months left of 2020 but this year has seen its fair share of major data breaches including:
Marriott International experienced another mega breach, when it was still recovering from the 2018 data breach that exposed approximately 339 million customer records
Zoom became a new favourite for hackers due to the remote working mandated in many parts of the world - in early April Zoom fell victim to a credential stuffing attack, which resulted in 500,000 of Zoom’s usernames and passwords being exposed on the Dark Web.
GoDaddy, the world’s largest domain registrar confirmed in April that credentials of 28,000 of its customer web hosting accounts were compromised in a security incident back in October 2019.
Nintendo - in March, users reported unauthorised logins to their accounts and charges for digital items without their permission. In June Nintendo advised that approximately 300,000 accounts were affected by the breach, resulting in the compromise of personal identifiable information such as email address, date of birth, country and gender.
Why this matters:
It has become evident that many of the recent data breaches were the result of credential stuffing attacks leveraging compromised passwords or passphrases. Credential stuffing attacks are automated hacks where stolen usernames and password combinations are thrown at the login process of various websites in an effort to break in. With billions of compromised credentials already circulating the Dark Web, credential stuffing attacks can be carried out with relative ease and with a 1-3% success rate.
When the account of an employee is compromised, hackers can gain access to sensitive data that organisation has collected, and sell it on the Dark Web. The stolen data, often including login credentials, can then be used to infiltrate other organisations’ systems which creates a never-ending cycle.
This is why the LinkedIn breach was blamed for several secondary compromises due to users recycling their exposed LinkedIn passwords on other sites.
Read more: https://www.infosecurity-magazine.com/blogs/credential-stuffing-recent-attacks/